First, create a Splunk integration in Torq as documented here. Make sure to set an authentication header. Note the endpoint URL, header name, and secret.
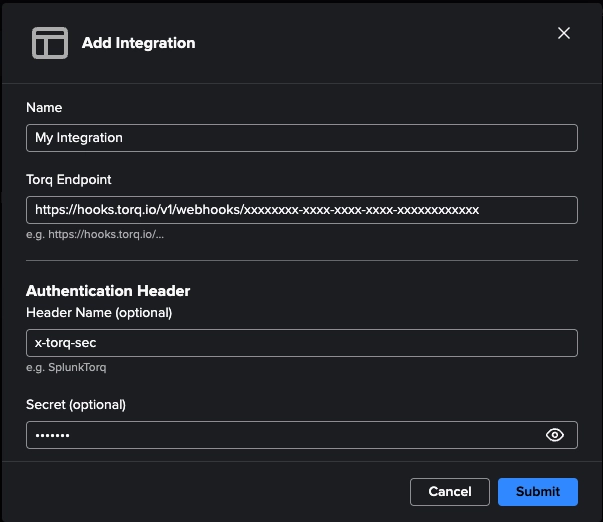
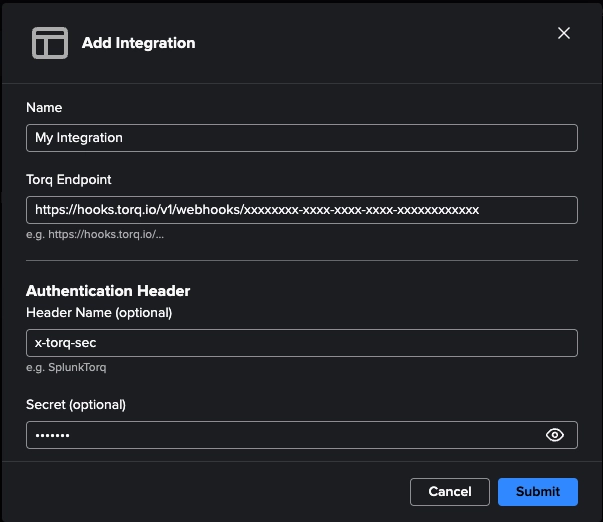
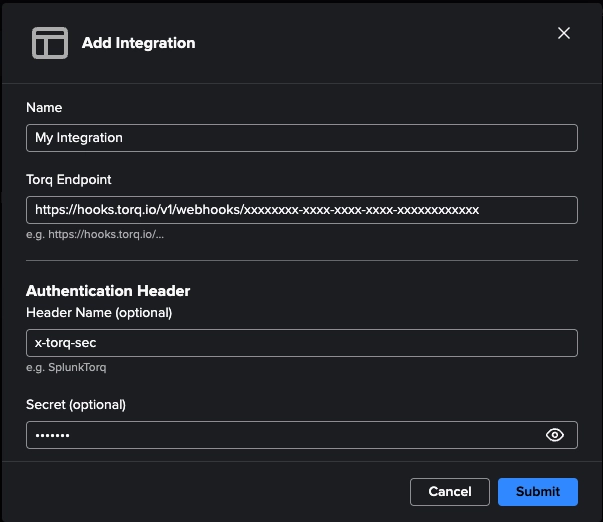
Next, in Splunk, navigate to the Torq Add-on for Splunk app. Click "Add integration" and enter the
endpoint URL, header name and secret you created in the previous step. Click save.
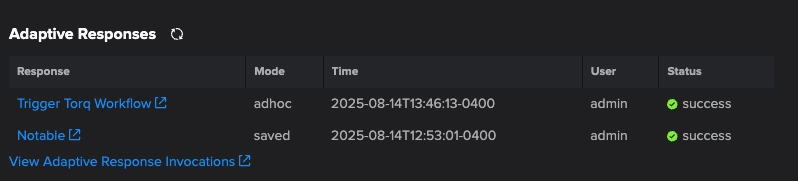
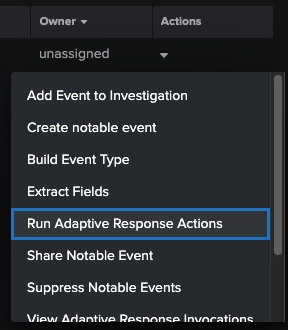
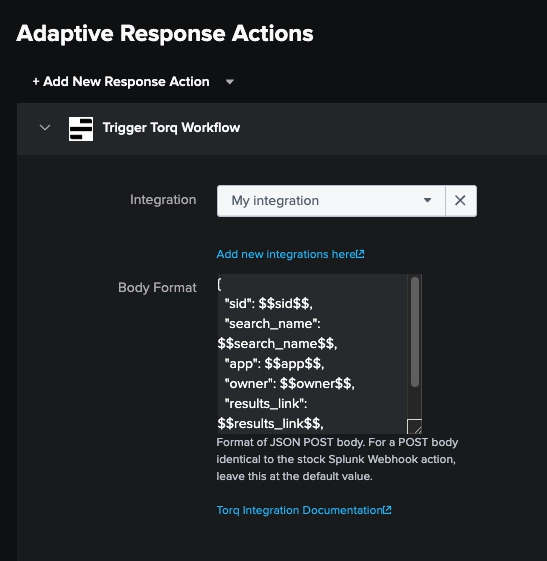
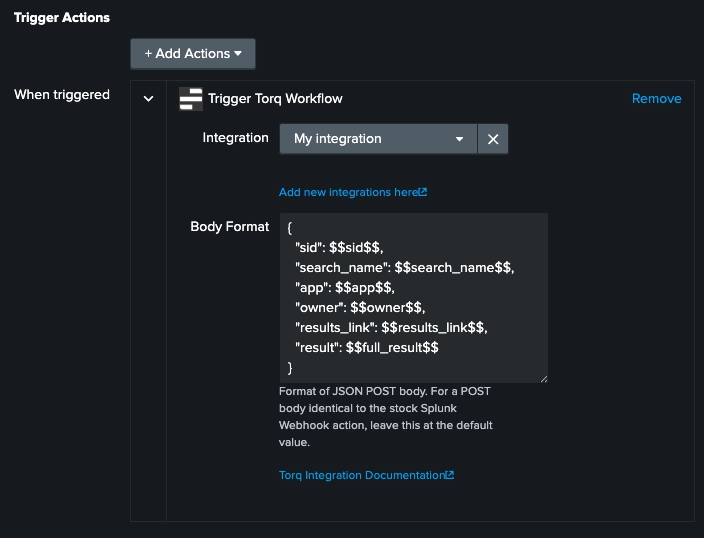
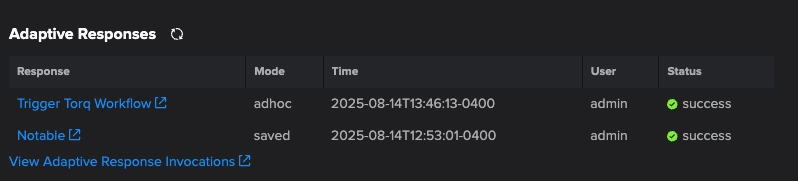
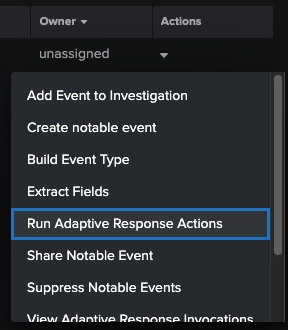
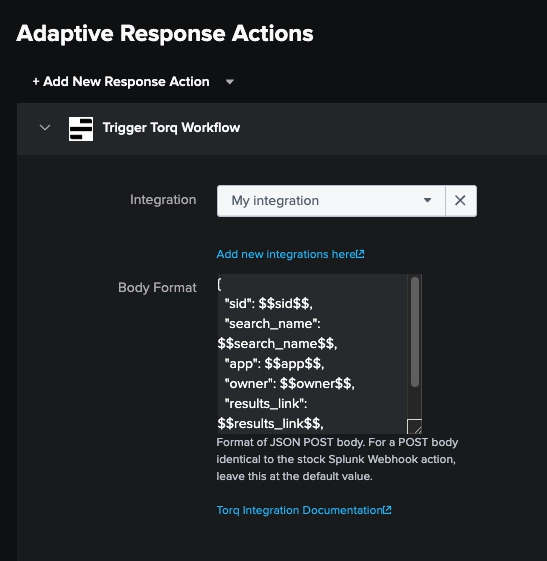
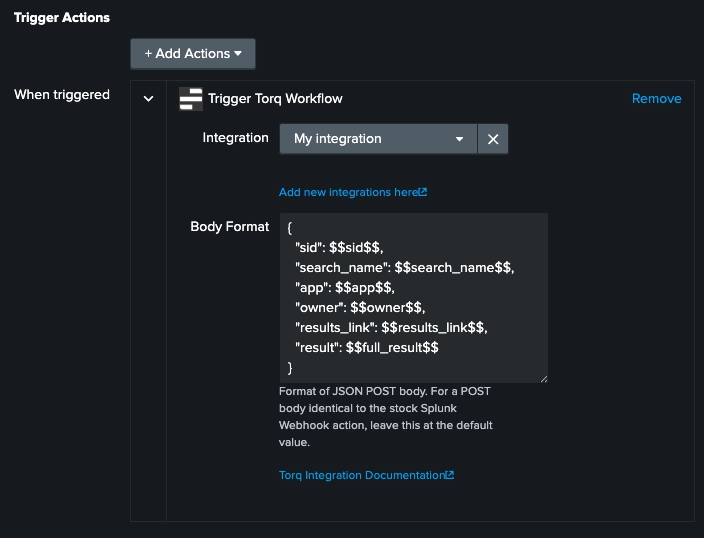
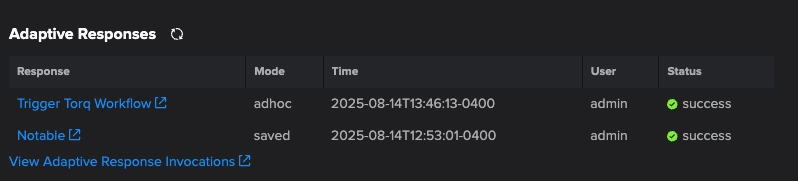
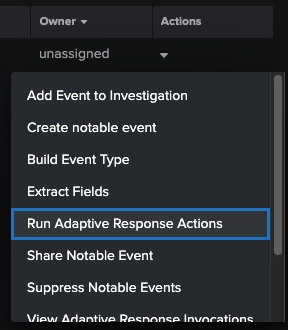
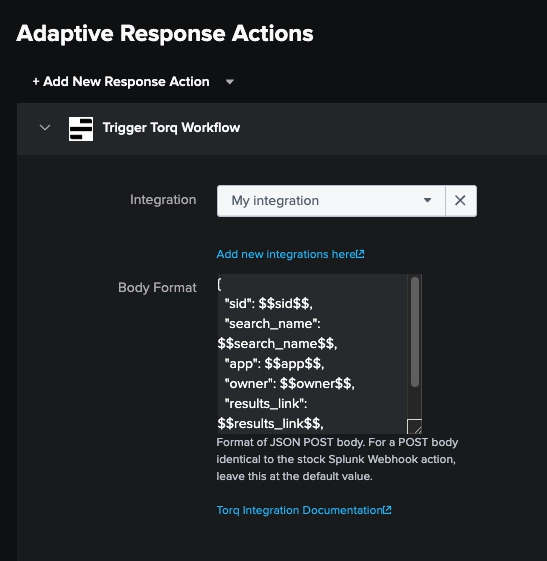
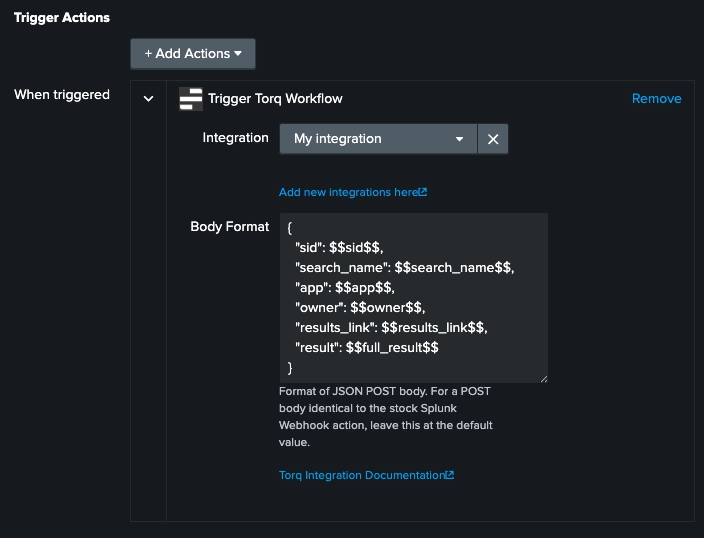
Now you can trigger your Splunk integration from an alert, correlation search, or ad-hoc as an adaptive response action.
Initial publication
As a Splunkbase app developer, you will have access to all Splunk development resources and receive a 10GB license to build an app that will help solve use cases for customers all over the world. Splunkbase has 1000+ apps from Splunk, our partners and our community. Find an app for most any data source and user need, or simply create your own with help from our developer portal.