The NetClean ProActive Threat Analysis Add-on for Splunk enables organizations to detect and respond to high-confidence indicators of human insider risk by classifying SHA-1 file hashes against NetClean’s ProActive Threat Intelligence API.
This add-on is designed to support security, compliance, and forensic teams by identifying known Child Sexual Abuse Material (CSAM) within enterprise environments. A positive classification represents a zero false positive signal and should be treated as a high-priority alert within existing incident response workflows.
By integrating this add-on into Splunk, organizations can operationalize CSAM detection as part of their broader threat detection and insider risk management strategy.
Once installed and configured, the add-on enables a streamlined detection and response flow:
Hash Detection
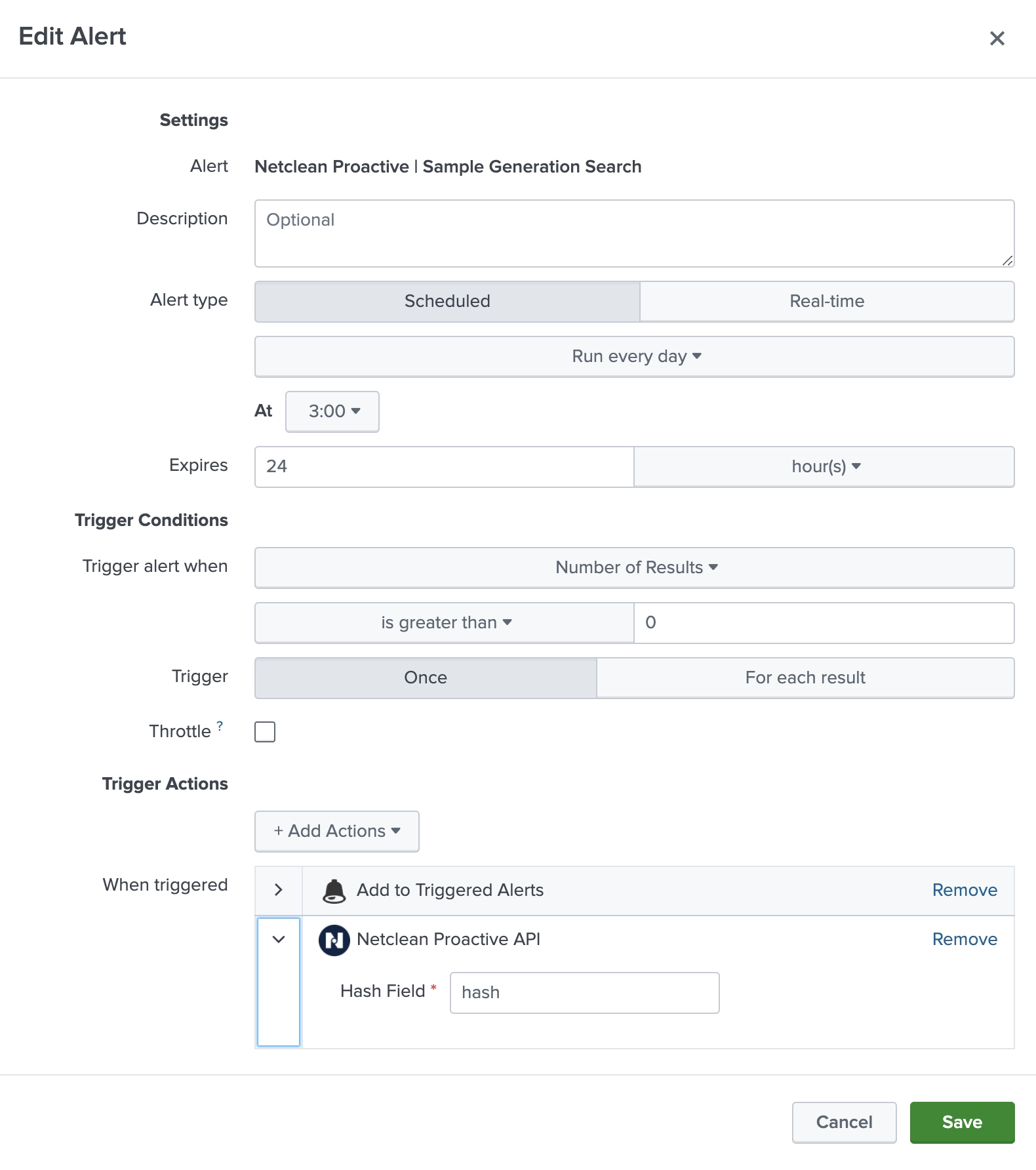
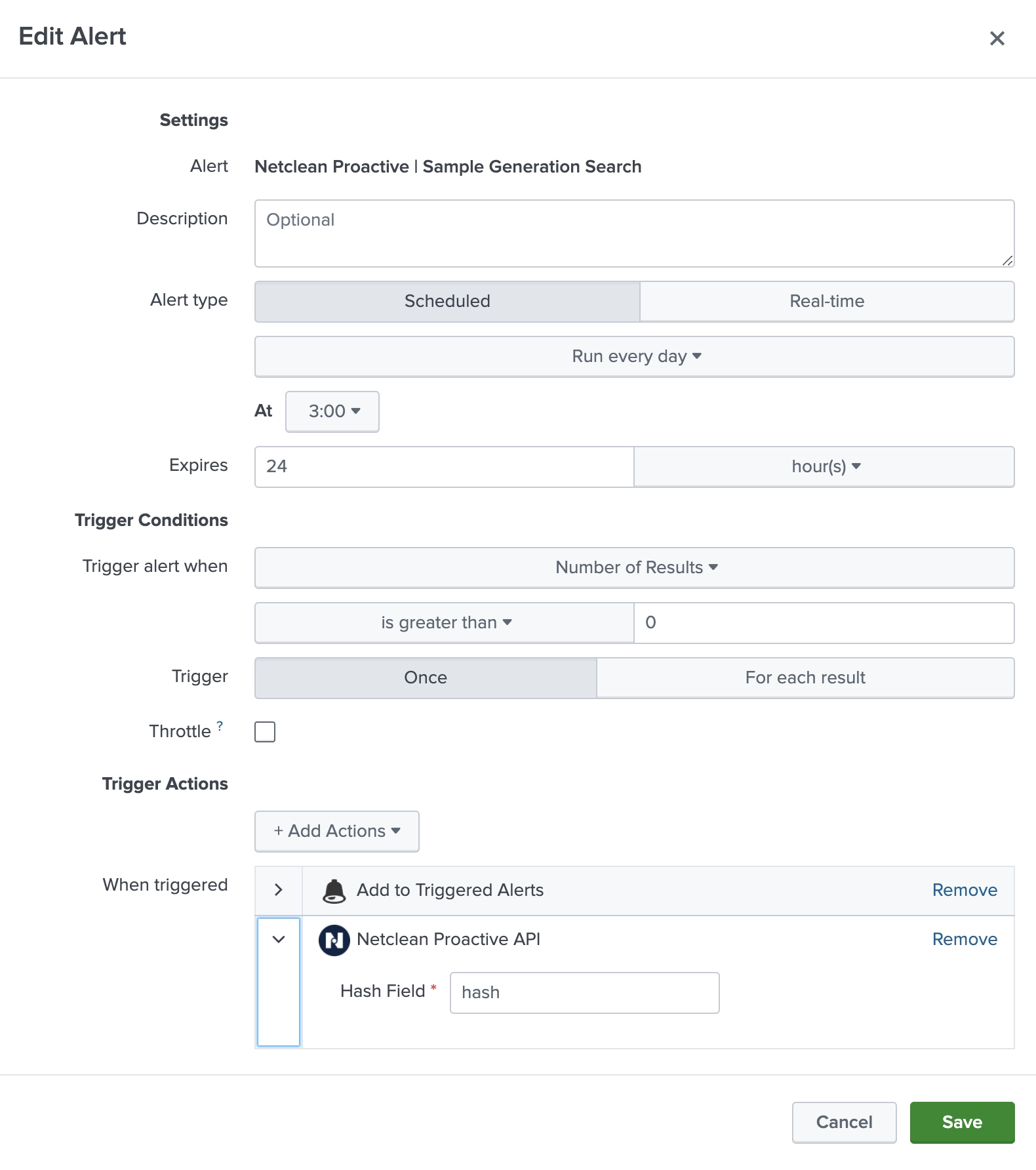
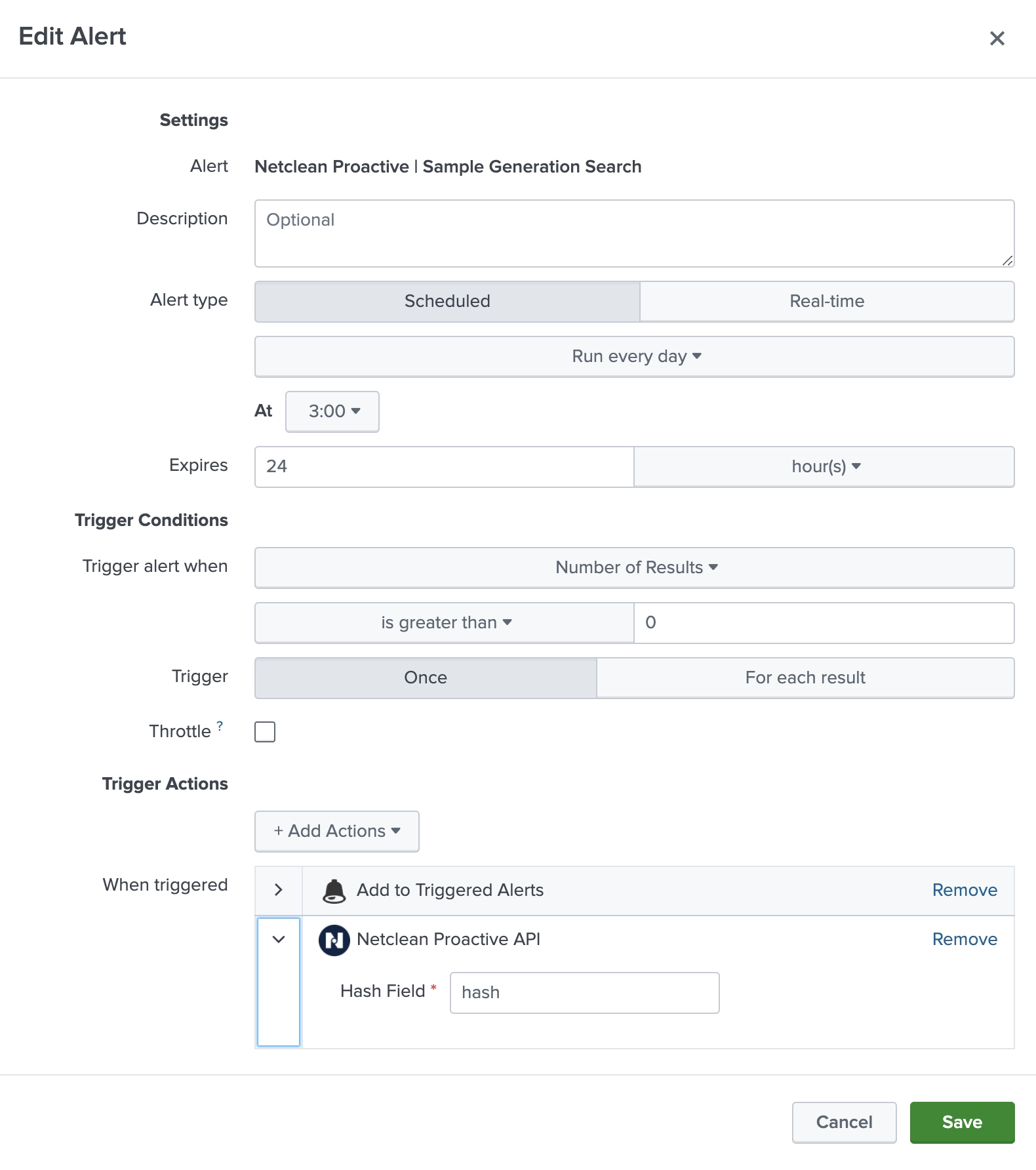
A scheduled or real-time Splunk search identifies SHA-1 file hashes in your environment (e.g., from endpoint logs, file scans, or DLP systems).
API Lookup
The add-on sends these hashes to NetClean’s ProActive Threat Intelligence API for classification.
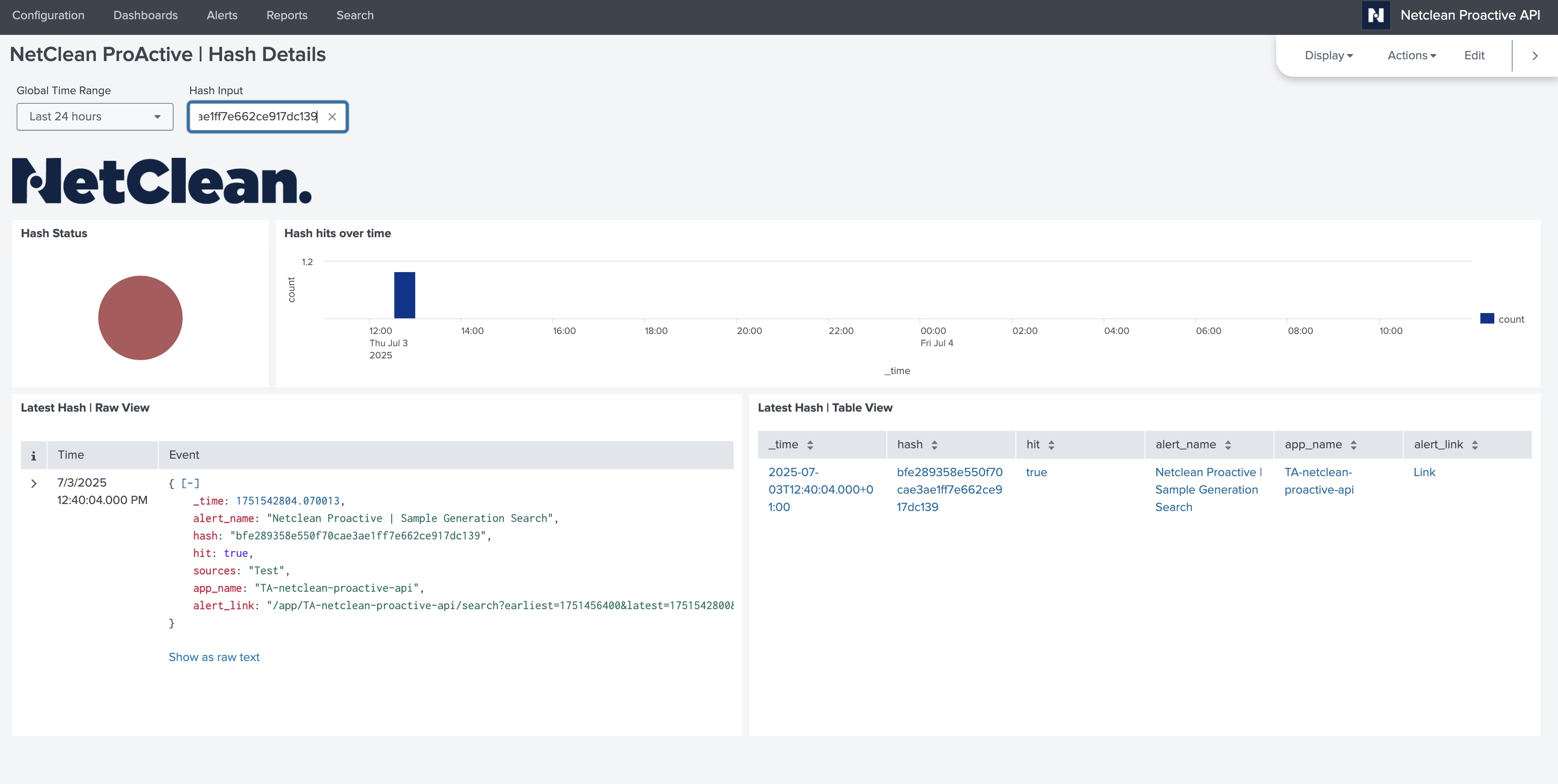
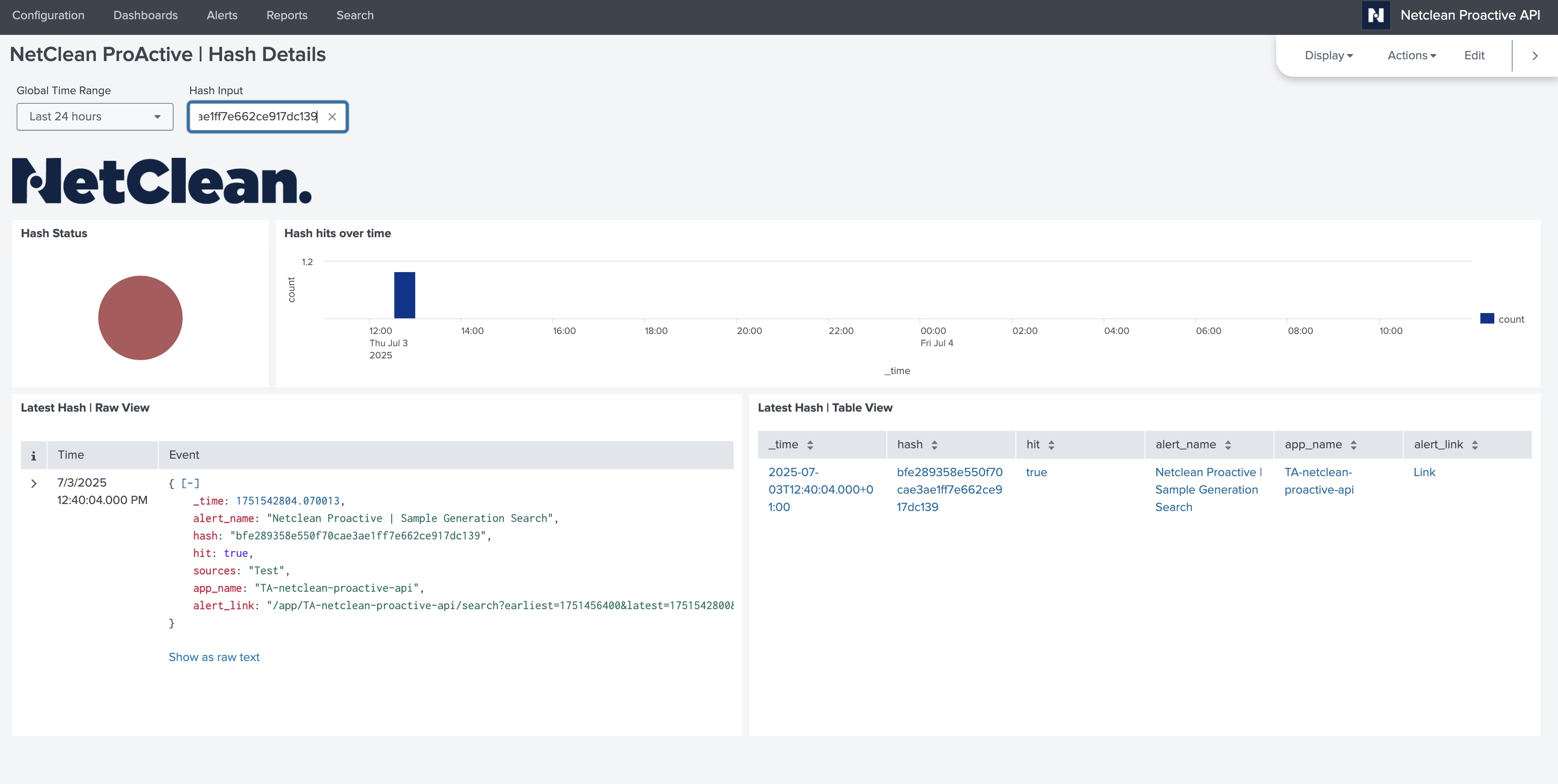
Classification & Indexing
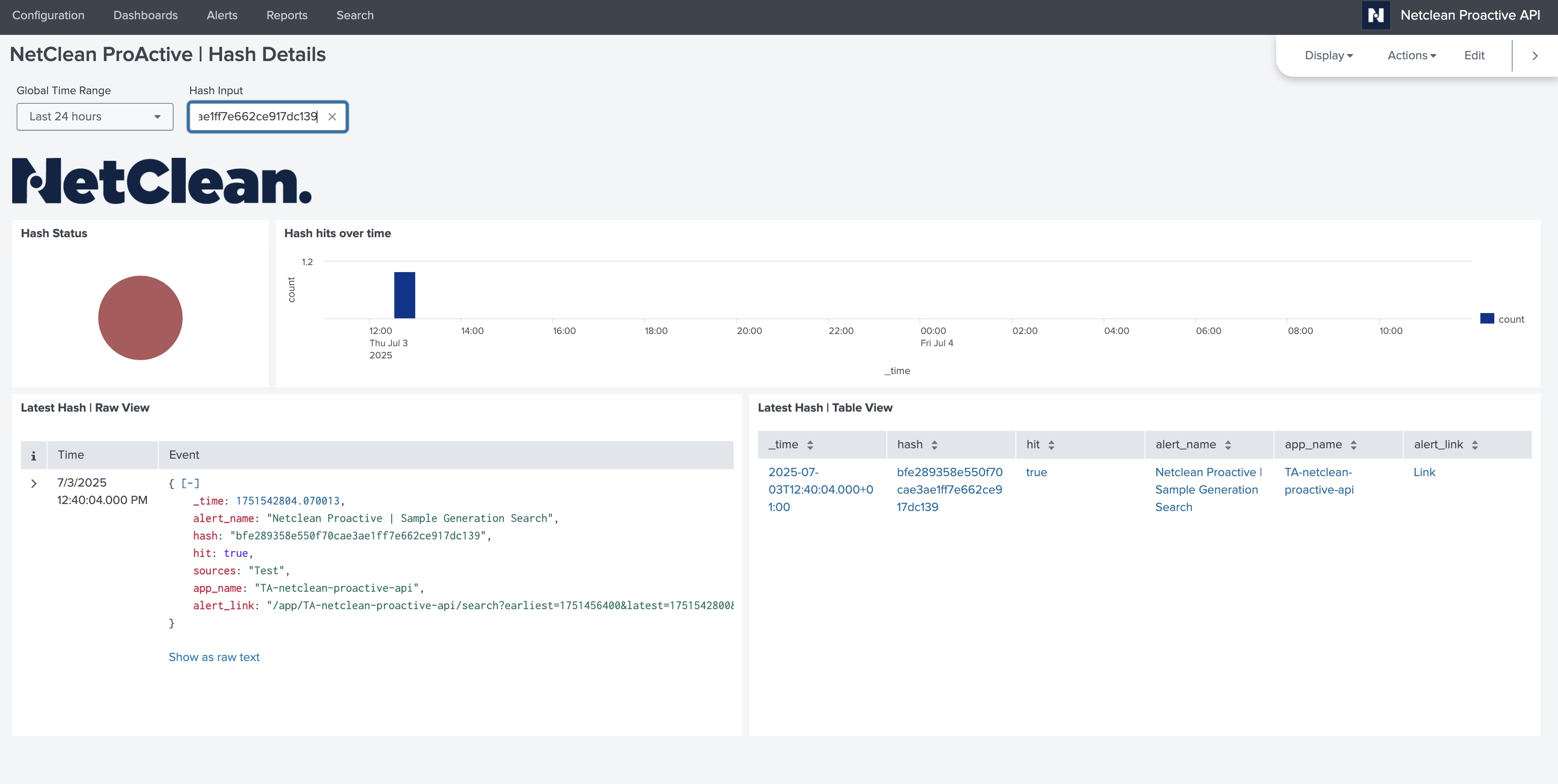
The API returns a result — “yes” (confirmed CSAM) or “no” — which is stored in a dedicated index along with contextual metadata.
Alerting & Response
A built-in alert (NetClean ProActive | Hash Found) can notify analysts via email when a hash is classified as CSAM.
The alert can be customized to trigger additional actions such as ticketing, SOAR playbooks, or escalation workflows.
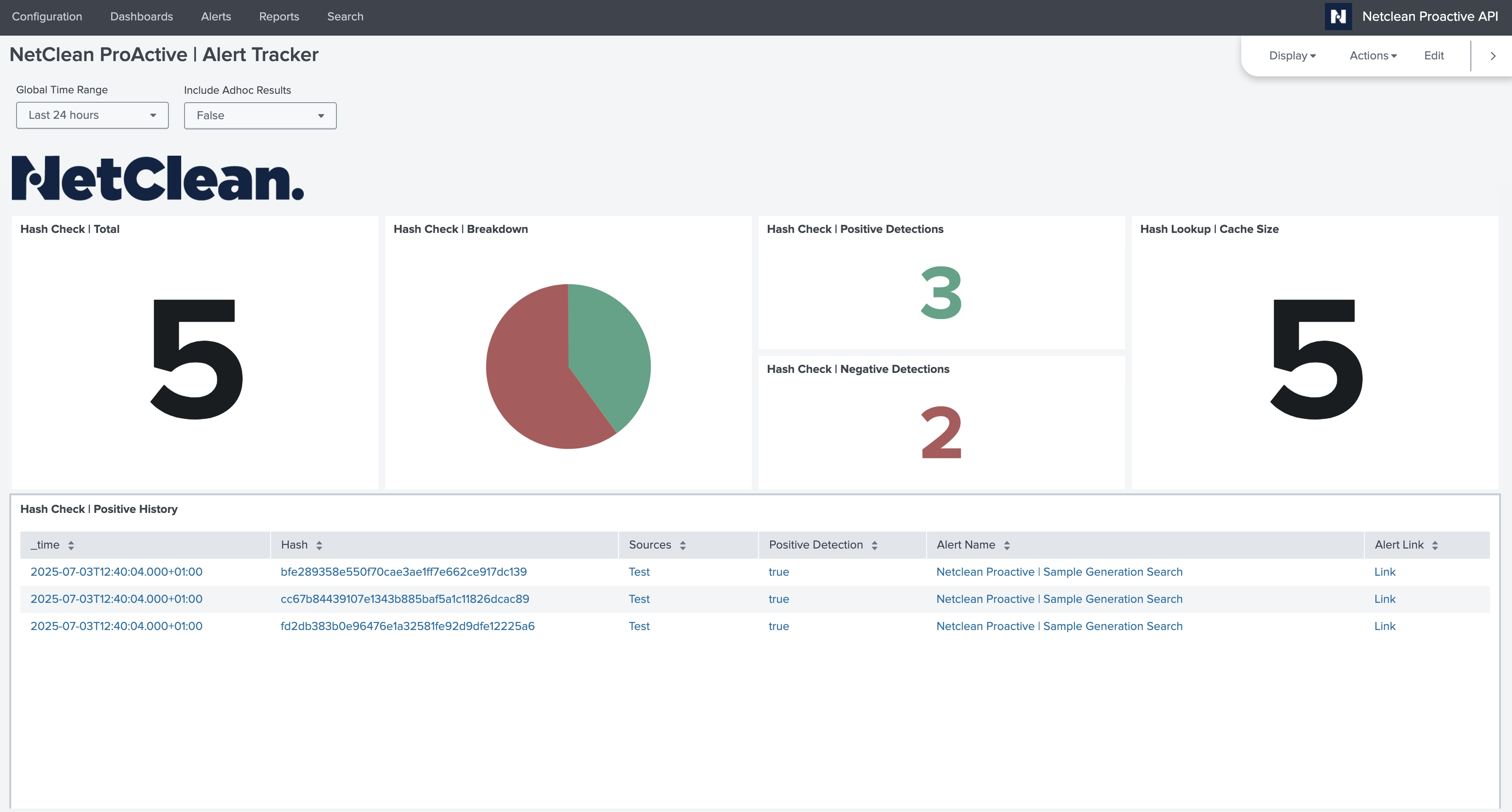
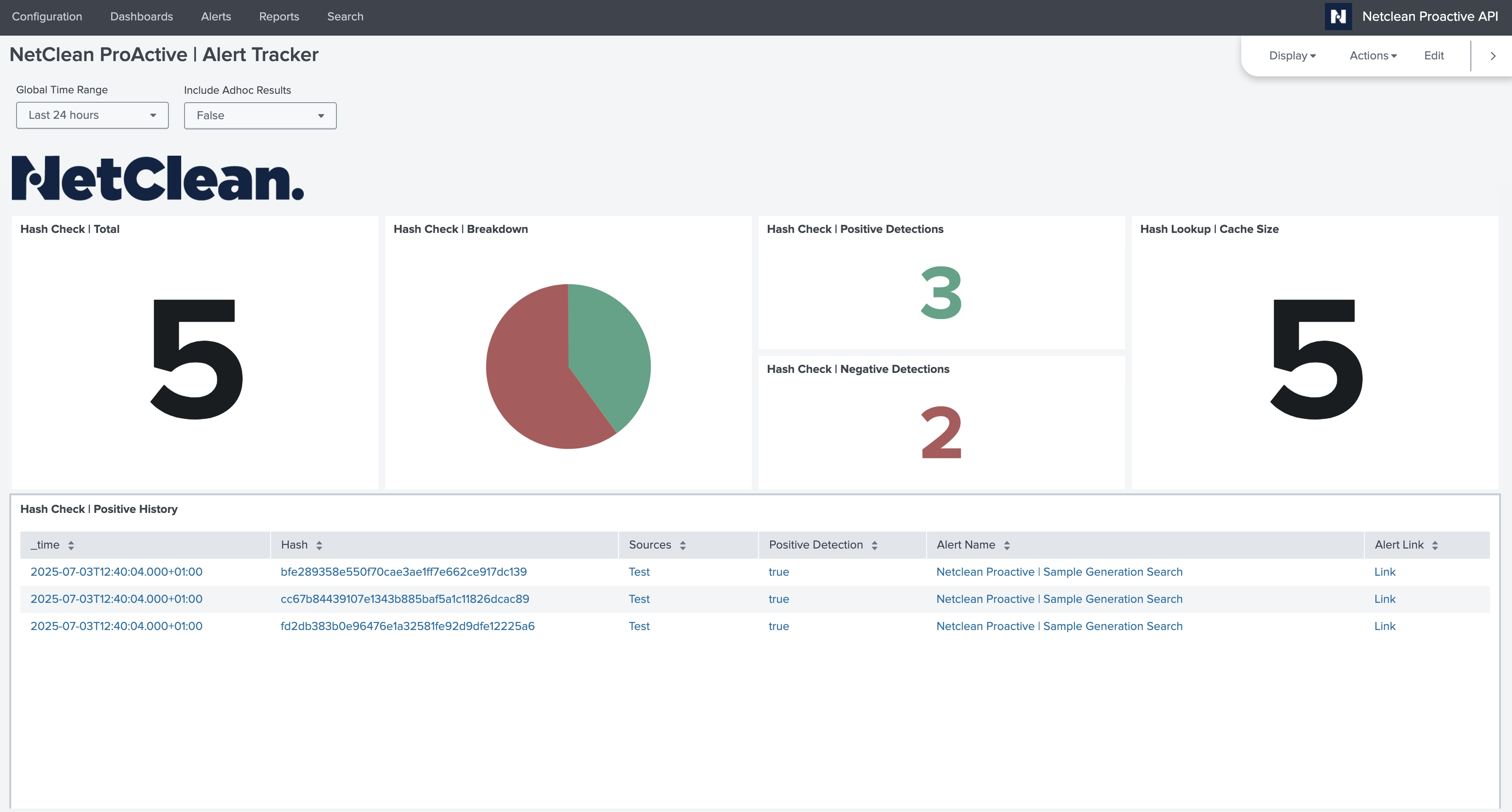
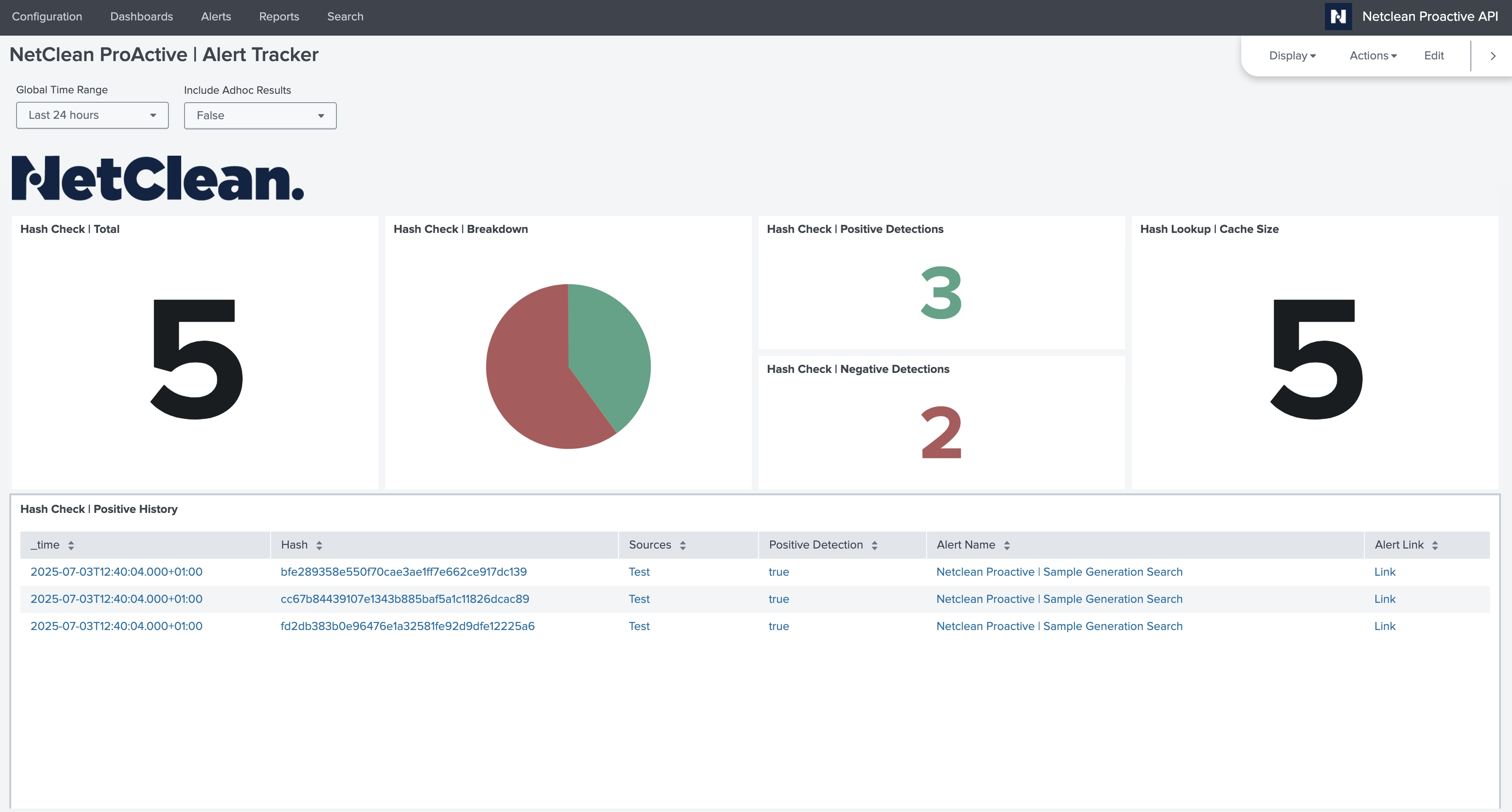
Visibility
All activity is visualized in the included Alert Tracker Dashboard, providing insight into alert history, trends, and errors.
A “yes” response from the NetClean Threat Intelligence confirms the presence of known CSAM — a verified and legally classified indicator.
This signal should be treated as a high-confidence, high-risk security event and integrated into your existing incident response processes.
This add-on requires a valid license for the NetClean ProActive Threat Intelligence API in order to function.
To obtain access, please contact NetClean Sales at:
📧 sales@netclean.com
A license is required to authenticate API requests and retrieve classification results. Without a valid license, the add-on will not be able to perform hash lookups or return threat intelligence data.
NetClean ProActive Threat Analysis Add-on for Splunk
Release Date: July 4, 2025
Author: NetClean
Supported Splunk Versions: 9.x
Supported Platforms: Splunk Enterprise (on-prem), Splunk Cloud
As a Splunkbase app developer, you will have access to all Splunk development resources and receive a 10GB license to build an app that will help solve use cases for customers all over the world. Splunkbase has 1000+ apps from Splunk, our partners and our community. Find an app for most any data source and user need, or simply create your own with help from our developer portal.