


Currently this app has detections for the rules listed here as organized by MITRE ATTACK MATRIX.
To install the app, follow the standard instructions from Splunk to install apps
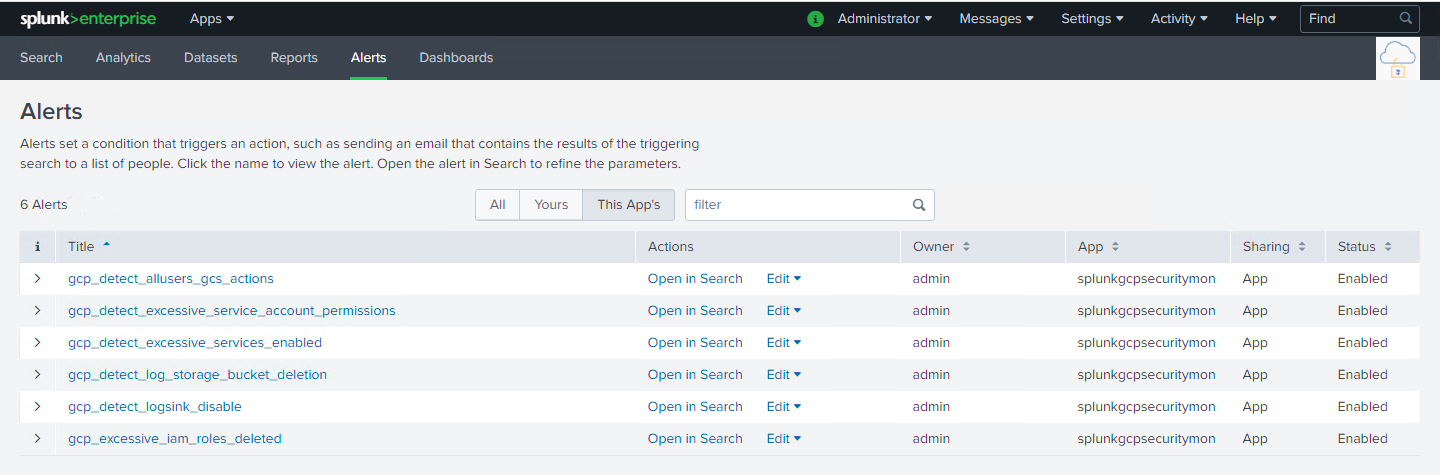
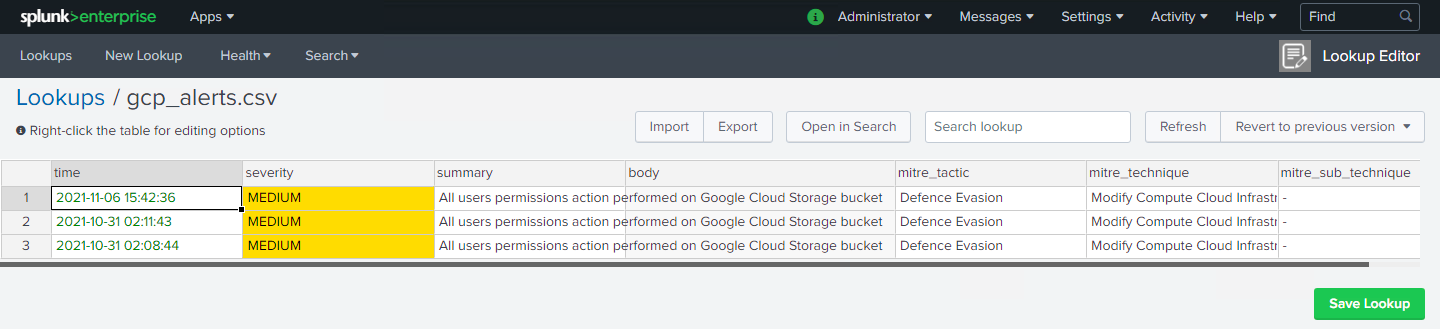
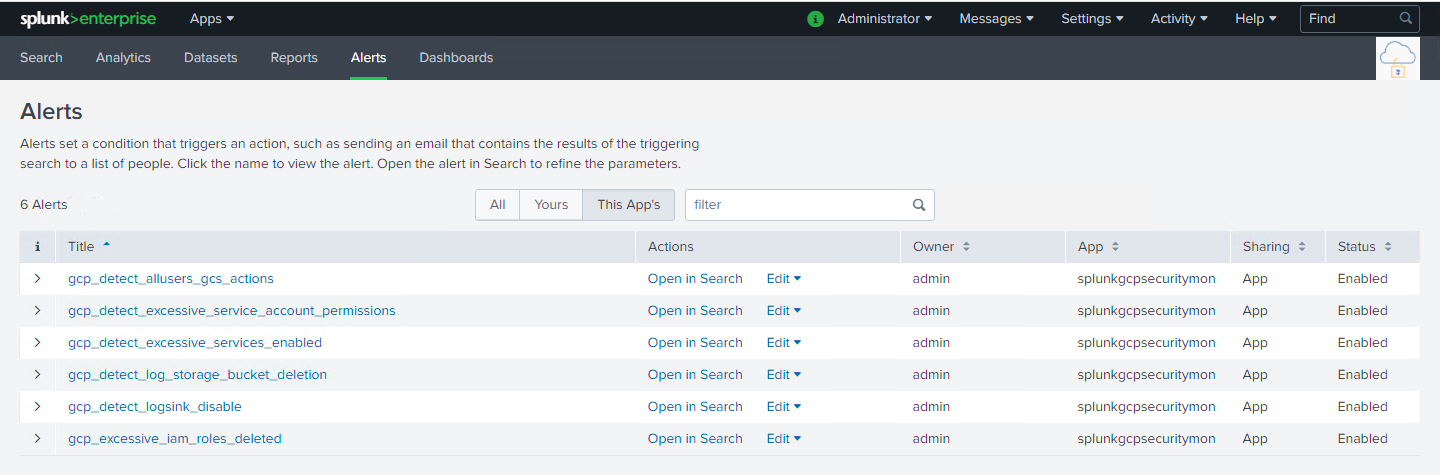
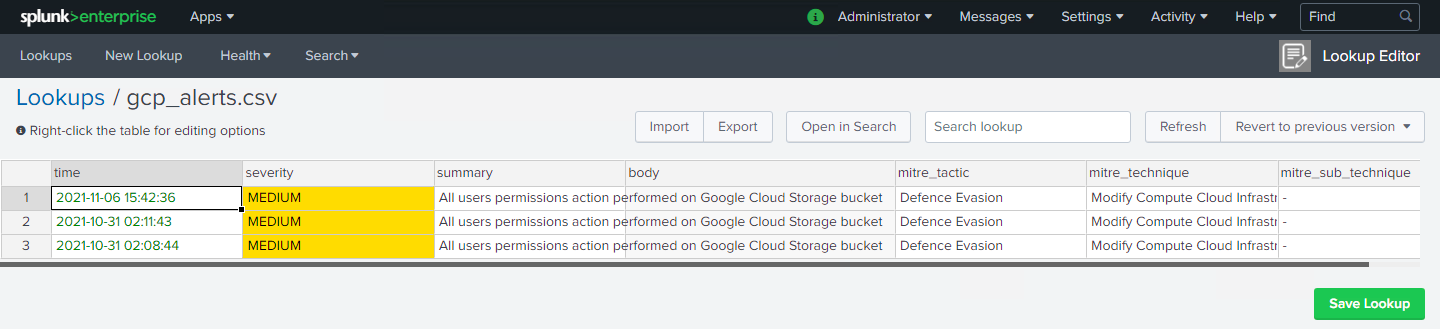
Currently alerting has been built for only a select set of rules above which function using individual Splunk advanced search macros. Each alert will append the detections generated (if any) to the Splunk lookup table gcp_alerts.csv
These are notes for this app developer's reference
Refer to the steps here
added new alerts - gcp_detect_clouddns_dnssec_disabled, gcp_detect_clouddns_logging_disabled
modified the definition gcp_log_search macro used across various alerts
Added the following additional alerts:
v1.0.0
Initial application with limited GCP rules:
- GCP - Detect allusers/allAuthenticatedUsers actions on GCS
- GCP - Detect excessive permissions assigned to service account
- GCP - Detect excessive services enabled
- GCP - Detect excessive IAM Roles deleted
- GCP - Detect logsink disabled
- GCP - Detect log storage bucket deletion
As a Splunkbase app developer, you will have access to all Splunk development resources and receive a 10GB license to build an app that will help solve use cases for customers all over the world. Splunkbase has 1000+ apps from Splunk, our partners and our community. Find an app for most any data source and user need, or simply create your own with help from our developer portal.