The Mandiant Advantage App for Splunk allows users to pull Mandiant threat intelligence into Splunk’s powerful data platform to stay ahead of attackers and threats. The app provides users a formidable combination of Splunk Enterprise Security’s (ES) powerful analytics, Splunk SOAR’s automation and massive scale along with Mandiant industry-leading threat intelligence, security validation and incident response.
Splunk ingests Mandiant intelligence, performs correlation and analysis, and provides dashboards for visualization. When combined, Splunk and Mandiant enable security professionals to validate their security stack and analyze security events through the eyes of Mandiant cyber security experts.
Maximize Mandiant Advantage with Splunk:
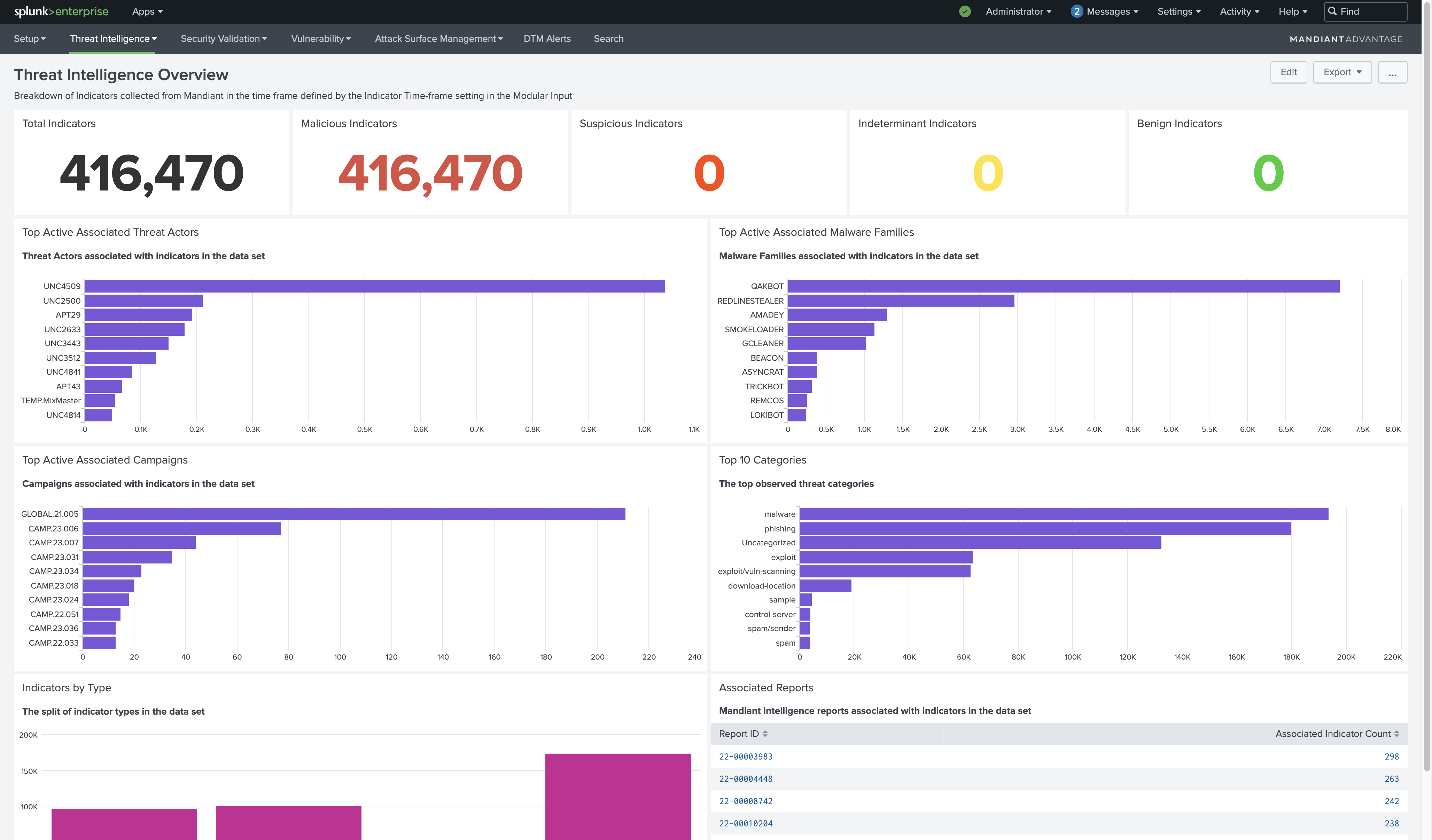
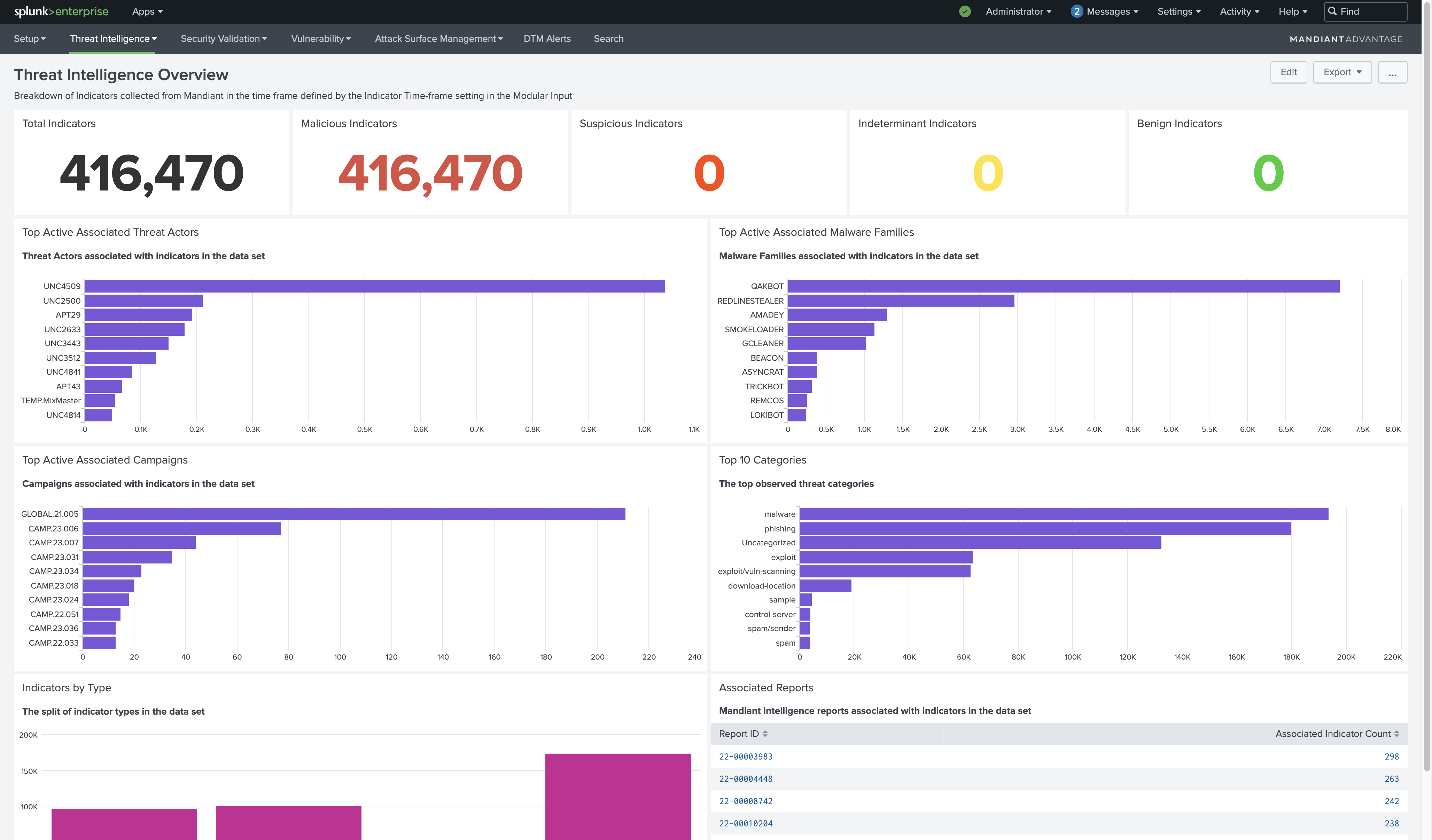
- Mandiant Threat Intelligence delivers the latest threat research directly to the SOC, allowing security teams to quickly see and detect real-time adversary activity. This empowers organizations to better understand the adversary and their tradecraft to make informed decisions and take decisive action. Mandiant intelligence feeds provide insights into well-known malicious actors, malware families, and map to MITRE ATT&CK for strategic response.
- Mandiant Attack Surface Management enables comprehensive visibility of the extended enterprise, so security teams can proactively mitigate real-world threats. Attack Surface Management scans corporate assets and cloud resources daily and identifies application and service technologies. The module assesses risks to the organization, assigns severity, and provides information security teams can use within Splunk to remediate.
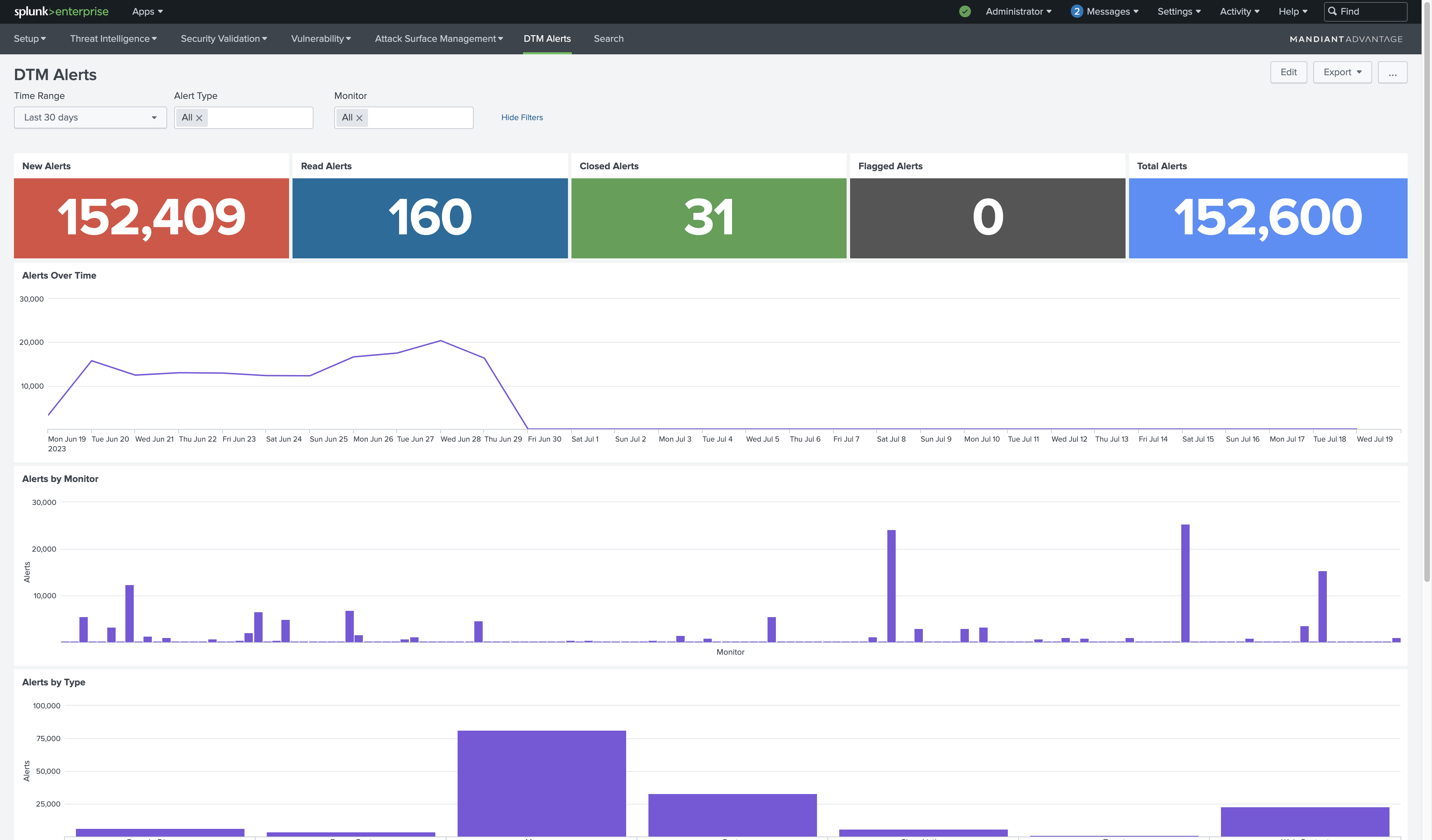
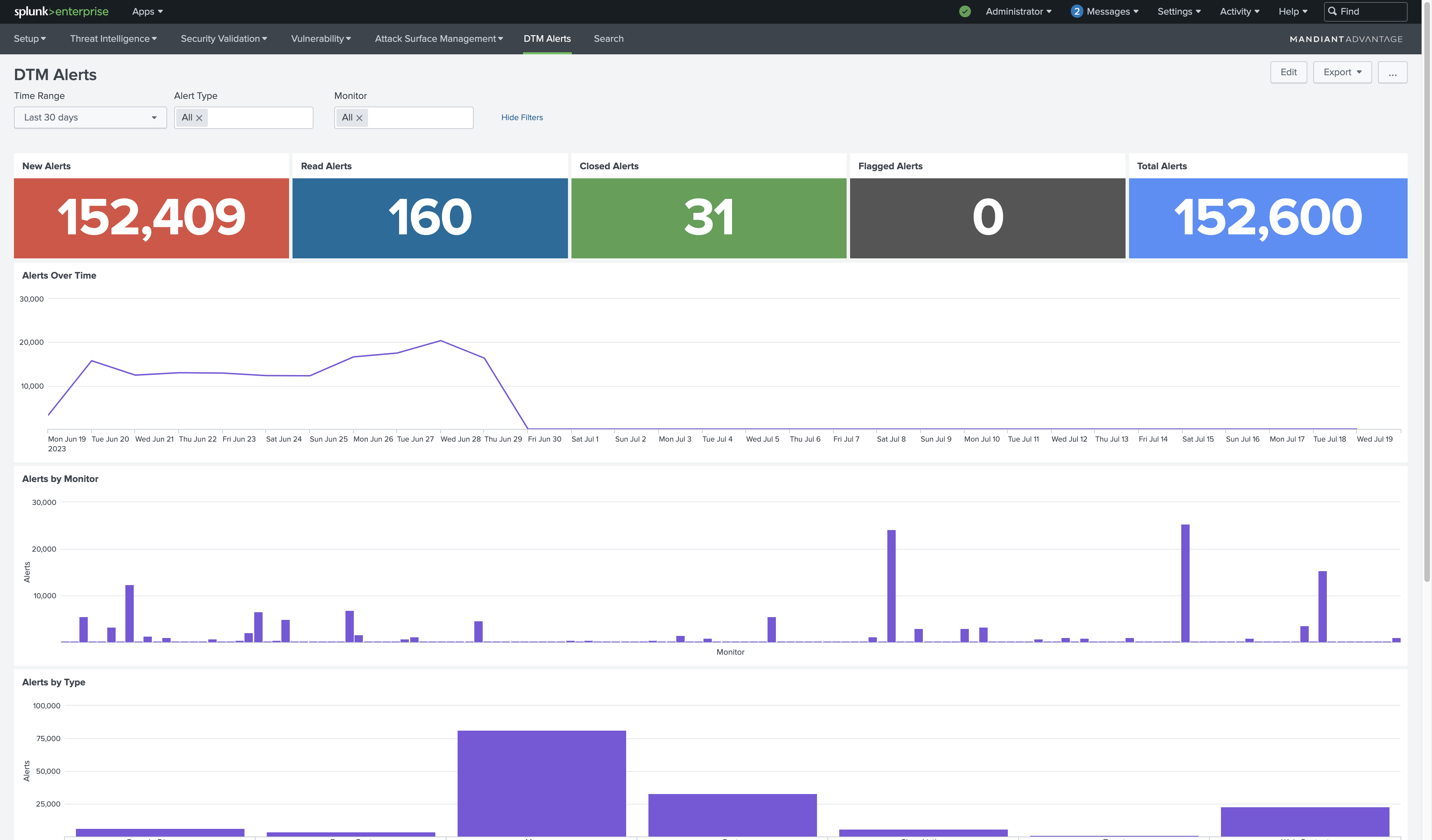
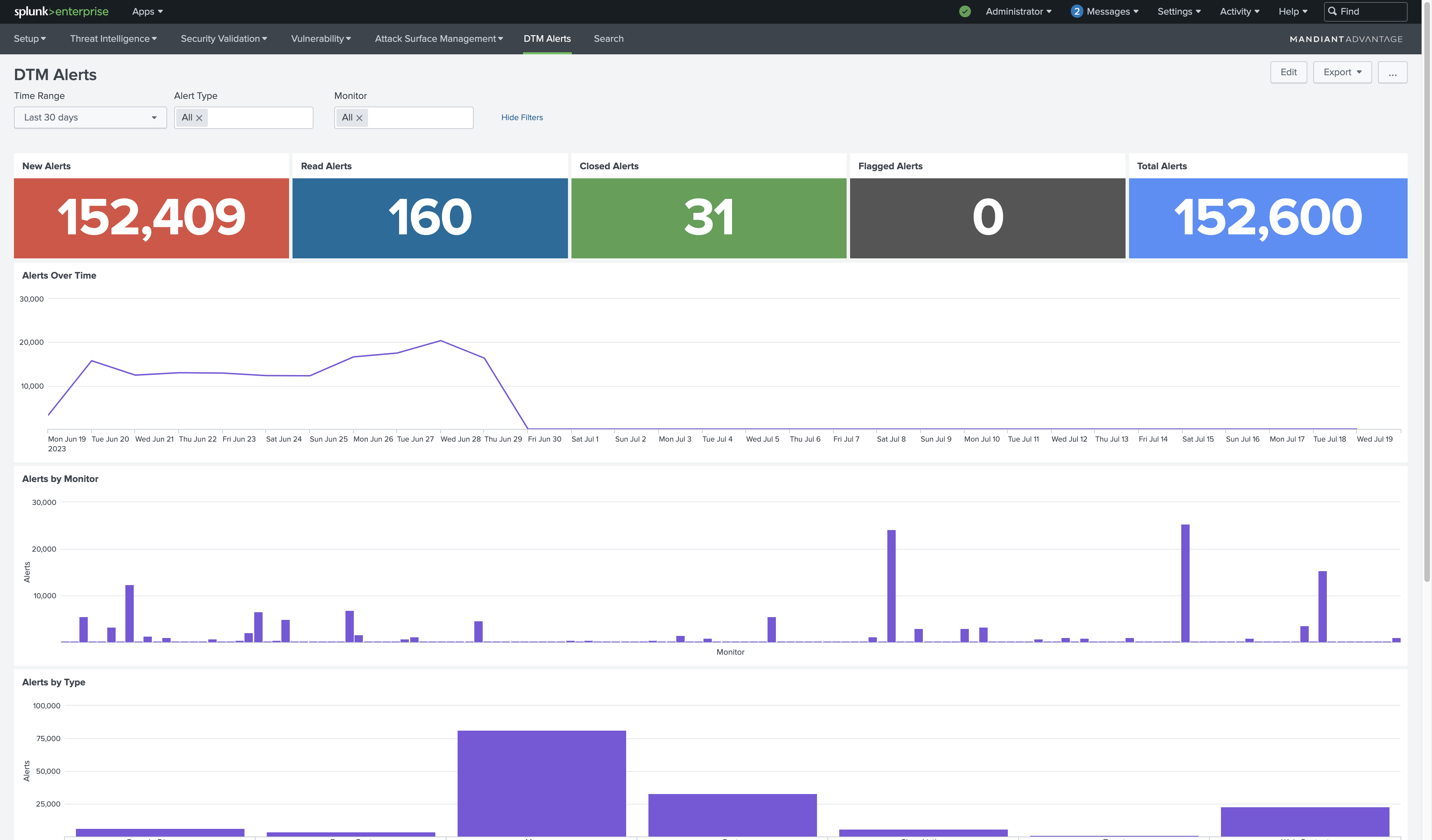
- Mandiant Digital Threat Monitoring delivers customized alerts on potential targeting and data or credential leaks. Triggered alerts from monitoring the surface, deep and dark web can be viewed in pre-configured charts via the Splunk visualization tool. These charts provide a high-level overview of alerts and bring what matters most to the forefront in Digital Threat Monitoring.
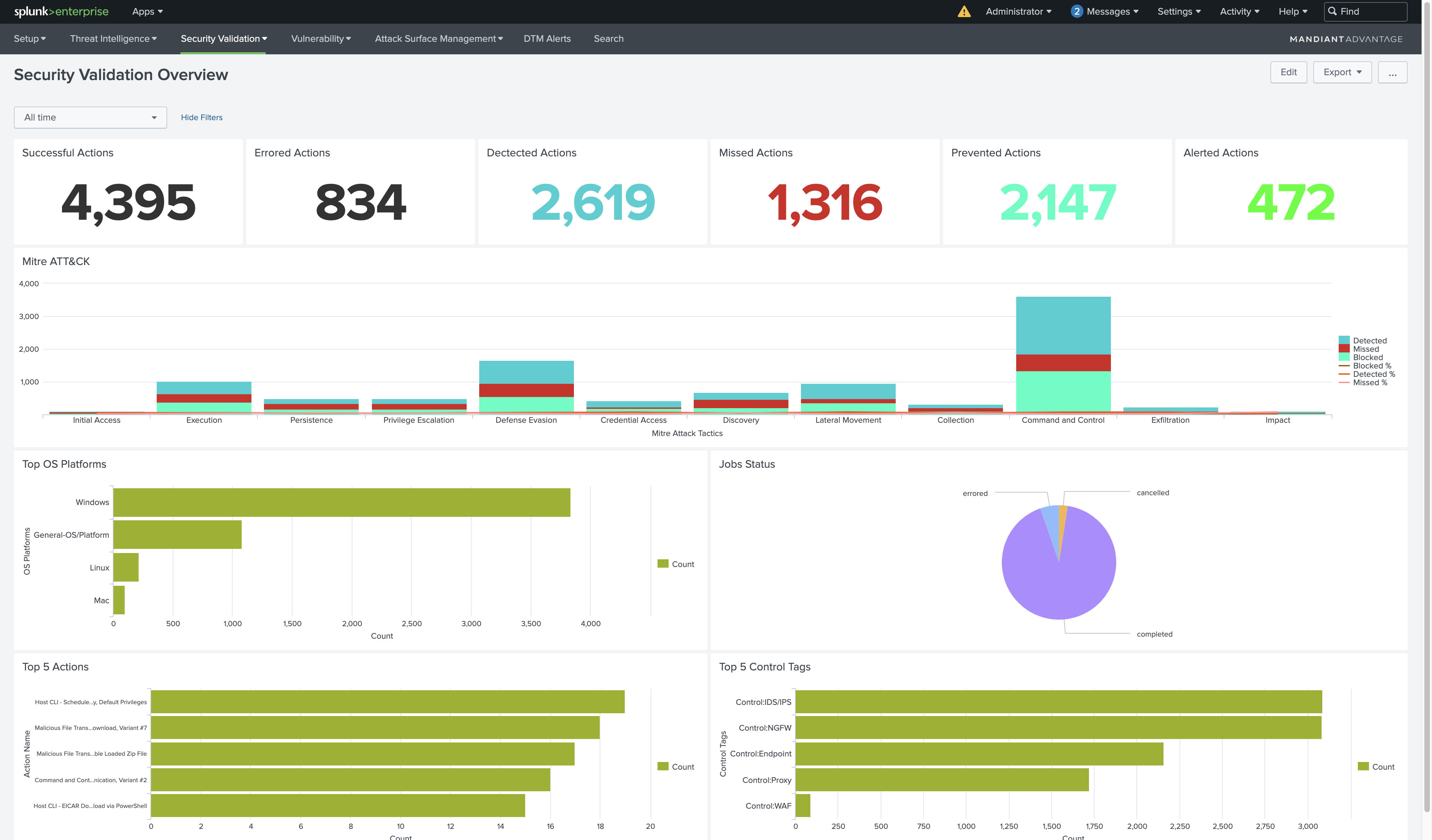
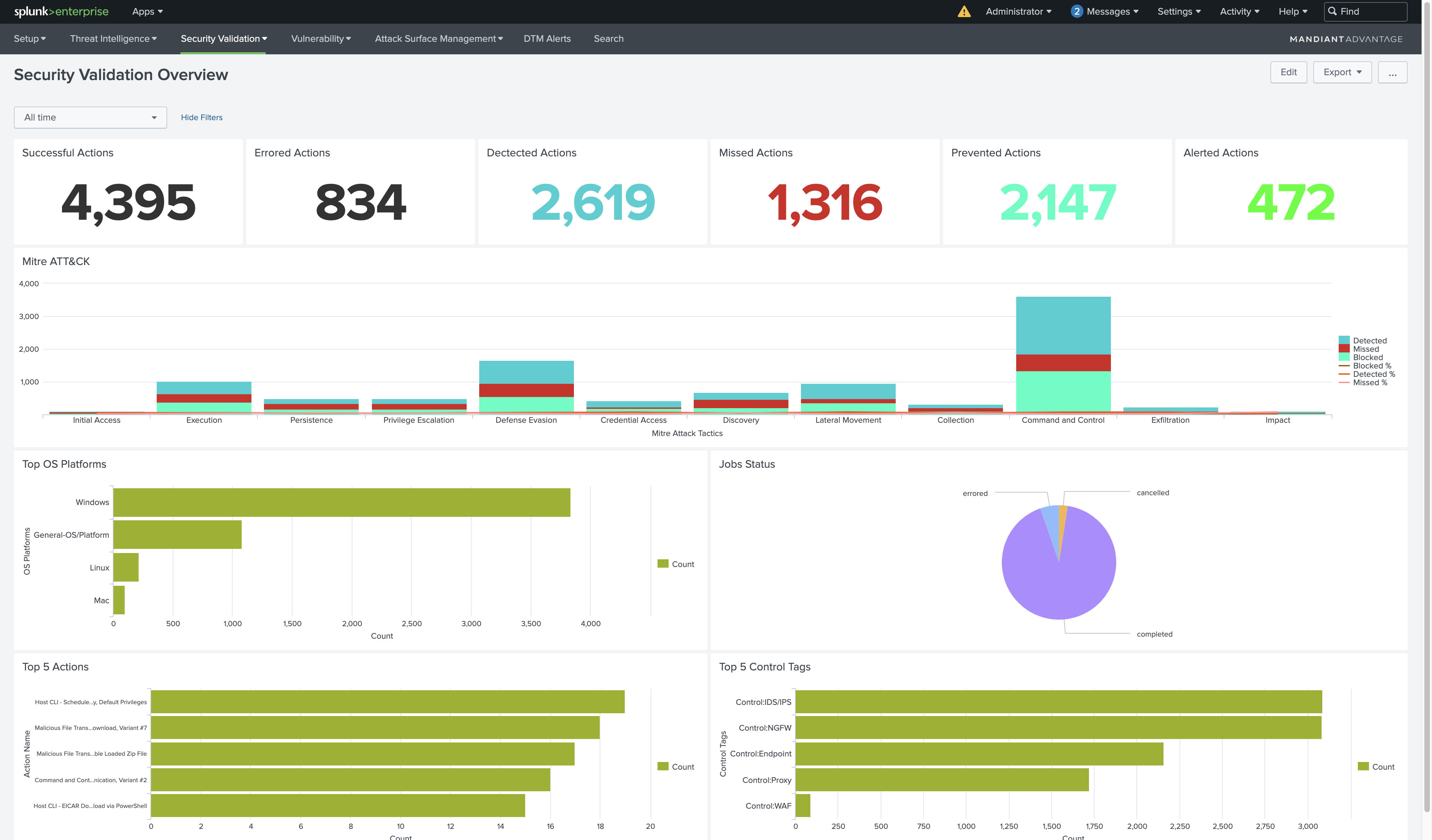
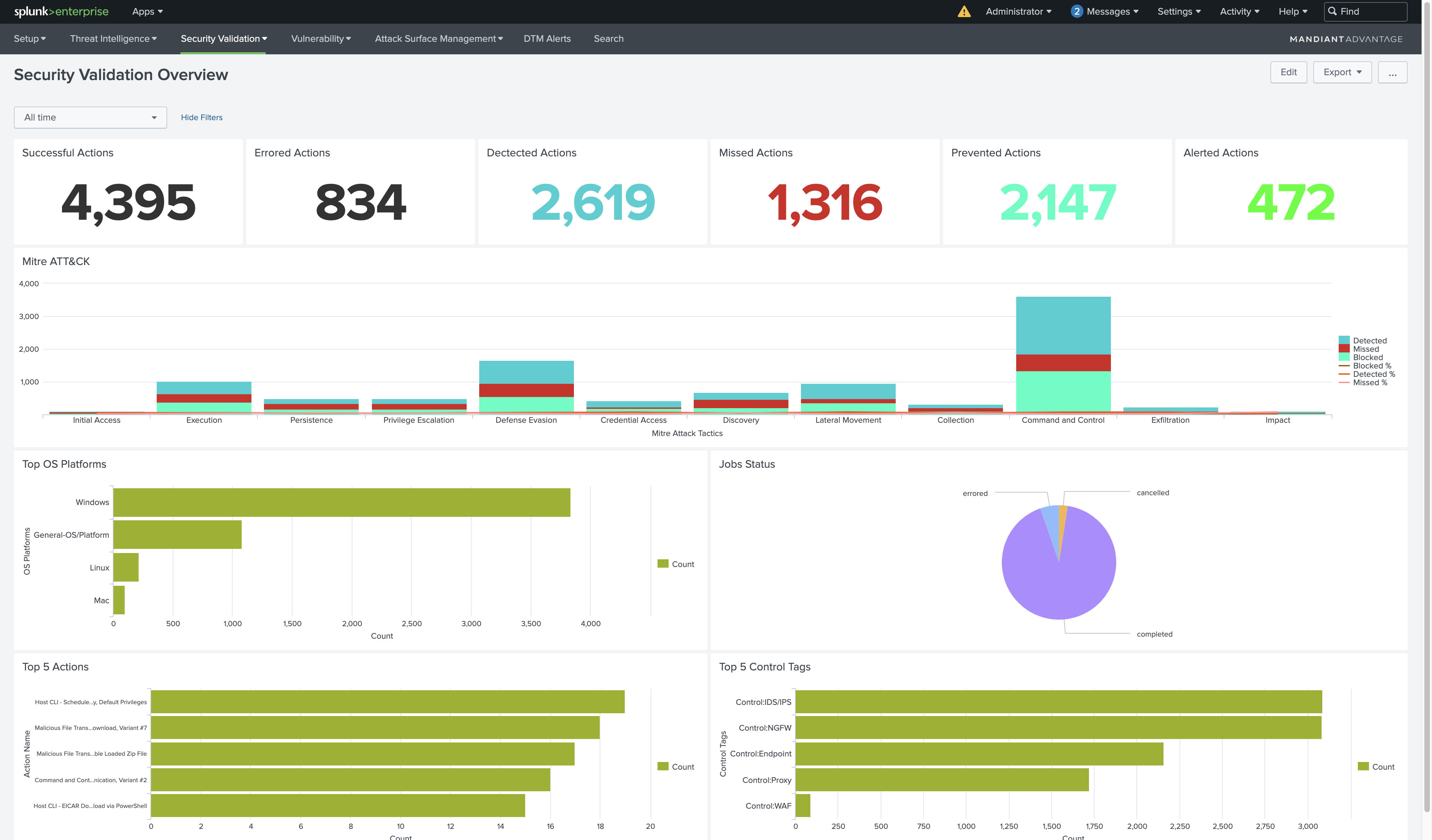
- Mandiant Security Validation allows customers to gain confidence in their readiness to withstand cyber-attacks. Mandiant tests the efficacy of control points to block attacks and validates that event information is being sent to and triggering alerts in Splunk Enterprise Security. With Mandiant and Splunk continuously validating the effectiveness of their cybersecurity controls, customers will have real data on how security controls are performing, allowing them to optimize their environments and make the right investments for the future.
- In the face of a suspected or active breach, customers can use the integration between Mandiant Incident Response and Splunk to engage with Mandiant incident response experts with the click of a button. These experts can help customers build their incident response capabilities, respond to active breaches, and bolster their security operations to detect and respond to attacks in the future.
Overview
The Mandiant Advantage App For Splunk pulls Mandiant Threat Intelligence, Security Validation Job telemetry, DTM alerts, and Attack Surface Management data from the Mandiant platform. The app performs correlation between Indicators of Compromise and security event data using Splunk CIM data models and provides dashboards to visualize data and alerts.
Compatibility
- Splunk version: 8.1.x and 8.2.x, 9.0.x
- Python version: Python3
- OS Support: Linux (Centos, Ubuntu) and Windows
- Browser Support: Chrome, Firefox and Safari